HIPAA compliance is non-negotiable in 2026, especially for healthcare apps. The stakes are higher than ever: healthcare organizations remain prime targets for cybercriminals – 77% were hit by ransomware in the past year – and data breaches are extremely costly. In 2025 the average healthcare data breach cost $7.42 million (and a record $10.22 million in the U.S.). A single breach can sink a startup or impose crippling fines and legal costs for an enterprise. Fortunately, building a HIPAA-compliant app is achievable with the right roadmap. This guide lays out a step-by-step plan, covering everything from secure architecture and cloud choices to encryption, audit logs, Business Associate Agreements, costs, and common pitfalls. By following these guidelines, you’ll not only protect patient data but also build trust – a key advantage in the competitive 2026 healthcare market.
What HIPAA Compliance Really Means for Apps in 2026
HIPAA (the Health Insurance Portability and Accountability Act) sets U.S. rules for protecting Protected Health Information (PHI). Although HIPAA was enacted in 1996, it remains the law governing patient privacy and security. Covered Entities and their Business Associates are legally bound to implement safeguards whenever PHI is created, received, maintained or transmitted. The last major HIPAA updates were driven by the HITECH Act (2009 Breach Notification Rule, 2013 Omnibus Rule), and as of 2024–2025 HHS has proposed further Privacy and Security Rule revisions. In practice today, compliance is about technical safeguards more than paperwork. For example, modern enforcement focuses on whether your systems encrypt and log data correctly, rather than solely on filing forms. The core idea is simple: any app handling patient health data must build privacy and security in by design, or risk severe penalties and loss of trust.
What Is HIPAA and Why It Still Applies in 2026
HIPAA’s Privacy and Security Rules establish standards for all PHI. The Privacy Rule gives patients the right to access their health records and controls how PHI may be used or disclosed. The Security Rule requires robust safeguards (administrative, physical, technical) to protect electronic PHI (ePHI). In other words, whether data sits on servers or smartphones, it must be guarded. Compliance isn’t optional: HHS Office for Civil Rights has ramped up enforcement in recent years, issuing hefty fines and breach notifications. Even though new HIPAA regulations (like NPRMs in 2024–2025) may be coming, current rules already demand that software developers lock down health data. In 2026, regulators expect healthcare apps to adapt to modern threats (AI misuse, cloud exposure, remote workers) and prove that safeguards are active, not just on paper.
PHI vs ePHI vs Consumer Health Data
It’s crucial to distinguish types of health data. PHI is individually identifiable health information created or received by a covered entity (doctors, hospitals, insurers, clearinghouses) or their business associates. ePHI is simply PHI in electronic form. If your app is tied to a healthcare provider or health plan, any patient data it handles is PHI/ePHI and falls under HIPAA. By contrast, consumer health data (like fitness, wellness, or genetic data collected by a direct-to-consumer app) is not PHI unless a covered entity is involved. For example, a telehealth video app used by a doctor’s office is HIPAA-covered, whereas a general fitness tracker on a user’s phone usually isn’t. The tricky cases are “gray areas” – e.g. health apps collecting data for insurers or research. If a health app developer processes PHI for a provider or partner, it becomes a Business Associate and must comply. In short, assume any patient-identifiable info tied to care or insurance is PHI; if your app touches that, HIPAA applies. (Conversely, standalone wellness apps handling only generic data are typically outside HIPAA’s scope.)
Which Apps Must Be HIPAA Compliant (And Which Don’t)
Not all health-related apps fall under HIPAA. The law applies when a covered entity or its vendor deals with PHI. Covered Entities include hospitals, clinics, physicians, pharmacies, insurers (HMOs, Medicare, etc.), and any organization that bills health care services. If your app is built by or for these entities – for example an EHR portal or medical records app – it must follow HIPAA.
Covered Entities Explained
HIPAA covers three main categories: healthcare providers (doctors, dentists, therapists, pharmacies, etc.), health plans (insurers, Medicare/Medicaid, HMOs), and healthcare clearinghouses (entities that process claims data). Thus, an app owned by a hospital for patient check-in or lab results clearly triggers HIPAA. Even apps by insurers (member portals, claims apps) must comply. Digital health startups can be covered too if they function as a virtual clinic or data processor.
Business Associates & SaaS Vendors
Any third-party that creates, receives, stores or transmits PHI on behalf of a covered entity is a Business Associate (BA). This includes SaaS vendors, cloud providers, app developers, analytics services, and device makers if they handle PHI. For instance, if you use AWS or Google Cloud to host PHI, they become a BA under HIPAA. HIPAA requires a signed Business Associate Agreement (BAA) with each BA. A BAA makes the provider legally liable to safeguard the PHI and outlines responsibilities. In practice, before using any third-party service (cloud databases, email platforms, SMS gateways, etc.), verify HIPAA eligibility and sign a BAA. (Major clouds all offer BAAs, but only for designated services – you must check which services are covered.)
Real-World App Examples
HIPAA-required apps: A telemedicine app built for a clinic, a patient portal for an insurer, or a remote patient monitoring app connected to a hospital’s systems. All of these create or use PHI as part of care or billing.
Non-HIPAA apps: A stand-alone meditation or fitness app that users download on their own – unless it’s directly connected to a healthcare provider – generally handles only consumer data and isn’t regulated by HIPAA.
Gray-area apps: For example, a lifestyle app that offers dietary advice but then shares data with an insurer may unexpectedly touch PHI. Many founders mistakenly assume “cloud = HIPAA safe” or overlook mobile-specific risks. In reality, as one expert notes, simply using AWS (even with a BAA) doesn’t make you compliant – you have to configure encryption, IAM, and logging correctly.
Also Read - Explore 16 Healthcare Software Types for UAE
Why HIPAA Compliance Impacts Your Product Roadmap
HIPAA affects product strategy in many ways.
For Patients: compliance is a trust signal. Patients must be informed (via Privacy Notice) how their data is used, and they have rights (access, correction, data portability). Incorporating consent management and transparent data handling fosters user trust and engagement. For example, features that let users see and control their data help meet HIPAA’s individual access rights. Compliant design (e.g. permission screens, audit logs visible to admins) shows you value privacy.
For Healthcare Businesses: the consequences of non-compliance are severe. Violations can trigger government audits and fines – even a single error can cost up to $50,000 or more per violation and up to $1.5 million per year for repeated breaches. OCR (HHS’s enforcement arm) regularly audits organizations and enforces actions. Beyond fines, a breach can spark class-action lawsuits, compliance mandates, and massive PR fallout. For startups, one public breach could destroy credibility overnight. Building compliance into your roadmap helps avoid these risks. (Tip: partner with expert healthcare software services early on. For instance, specialized healthcare software services can guide you in embedding compliance without delaying features.)
HIPAA Rules Every App Owner Must Understand
Three core HIPAA rules are critical for app developers:
HIPAA Privacy Rule
This rule governs what PHI you can collect, use, and share. It grants patients the right to access their records and dictates that any use of PHI beyond treatment, payment or healthcare operations generally requires patient authorization. In practice, this means your app must enforce policies on minimum necessary access and record patient consents. For example, if your app shares data with a research partner or marketing entity, it must obtain explicit authorization from the user. Ensure your app has user login screens, privacy notices, and consent checkboxes for any non-routine data sharing. (By law, patients can also request copies of their data – your app should support data export or viewing functions.)
HIPAA Security Rule
The Security Rule lays out safeguards for ePHI. It mandates administrative, physical, and technical controls. Administrative safeguards include risk assessments, policies, and staff training (covered in later sections). Physical safeguards mean things like locked servers or secured data centers. Technical safeguards are most visible in an app: they include access controls (unique user IDs, authentication), encryption, and audit controls (system logs). In short, you must assume the data is a prime target and build defenses accordingly. For example, implement robust user authentication (each user gets a unique login and role), encrypt all PHI in transit and at rest, and ensure that only authorized users can see specific records. The Security Rule also emphasizes the “CIA triad” – confidentiality, integrity, availability – so design features (like backups and checksums) to uphold those.
Breach Notification Rule
If unsecured PHI is impermissibly disclosed, HIPAA’s Breach Notification Rule kicks in. This means timely notifications: affected individuals, HHS OCR, and sometimes the media must be notified without unreasonable delay and no later than 60 days after discovery. Your app and backend systems must be able to detect a breach and alert your compliance team immediately. Failing to notify on time can compound penalties. In practice, this means having an incident response plan, a way to identify which records were exposed, and templates for the required notices. Also, if a Business Associate (e.g. your cloud host or analytics vendor) suffers a breach, they must notify you within 60 days so you can in turn notify patients.
Step-by-Step: How to Build a HIPAA-Compliant App
-
Choose a HIPAA-Compliant Architecture. Decide early whether to use cloud hosting, on-premises servers, or a hybrid model. All can be HIPAA-compliant if done right. On-prem gives full control but requires heavy investment in physical security. Cloud (AWS, Azure, Google) offers HIPAA-eligible services under a shared responsibility model: the provider secures the infrastructure, you secure the application. Regardless, modern best practice is a zero-trust model: never implicitly trust any network component. As industry experts advise, assume “every connection is potentially hostile” and verify identity each time. Use network segmentation, VPNs or secure access service edge (SASE) solutions for remote access, and enforce per-application firewalls and gateways.
-
Select a HIPAA-Compliant Cloud Provider. If you use cloud, pick one with HIPAA support. AWS, Microsoft Azure, Google Cloud and others can support HIPAA apps when properly configured and under a signed Business Associate Agreement (BAA). Each offers lists of “HIPAA-eligible” services (compute, databases, email, etc.) that fall under the BAA. Before storing any PHI, sign a BAA with the provider. The BAA typically makes the provider a Business Associate, meaning they’ll handle physical security but you remain responsible for application-level security (encryption, IAM, logging). In short, no cloud is “HIPAA-certified out of the box” – you must enable encryption keys, access controls, and monitoring yourself.
-
Design Secure Data Flow (PHI Separation). Architect the app so PHI only flows where absolutely needed. For example, keep PHI data on the backend servers and only render minimal info in the frontend. Do not send PHI to analytics or logging tools. Use tokenization or de-identification when possible. Isolate logs, metrics, and backups to avoid them accidentally capturing sensitive fields. For instance, use user IDs (not names) in logs and never log full medical records. Apply network segmentation so the database handling PHI is on a separate private subnet with strict firewall rules. Wherever possible, follow the “minimum necessary” principle: each component only accesses the smallest data subset it needs. This reduces risk if any part is compromised.
-
Encrypt Data Everywhere. Encrypt all PHI both in transit and at rest. Use TLS 1.3 (HTTPS) for every API and web connection. On servers and devices, encrypt databases and storage with strong ciphers (e.g. AES-256) and manage encryption keys securely. According to HHS guidance, encryption is one of the technologies that renders PHI unreadable, relieving you from breach notification obligations if implemented properly. For example, enable full-disk encryption on servers and use envelope encryption for files. For cloud services, turn on built-in encryption (and manage keys yourself or via a key management service). Don’t forget backups: encrypted backups ensure that even if media are stolen, data remain safe. As a rule, assume encrypted data is “secured PHI,” which significantly mitigates breach risk.
-
Implement Strong Identity & Access Controls. Strictly control who can see or modify PHI. Require unique user IDs and multi-factor authentication (MFA) for all accounts, especially administrators. (As experts note, MFA is “non-negotiable” – it stops over 99% of automated credential attacks.) Enforce strong passwords or biometrics, and implement role-based access control (RBAC) so users only access data necessary for their role. For instance, doctors see only their patients; patients see only their own records; auditors see logs but not health details. Include an emergency break-glass process (with separate audit logging) for urgent access. Also implement automatic session timeouts and auto-logoff after a short inactivity period. This prevents PHI exposure if a user forgets to log out.
-
Enable Audit Logs & Monitoring. Turn on detailed logging for every access to PHI. Logs must capture who, what, when, and where: user IDs, timestamps, IP addresses, and actions (view, edit, delete). HIPAA requires retaining audit logs for at least six years using tamper-proof methods (e.g. WORM storage or cryptographic hash). In practice, use a centralized logging system (e.g. Splunk, ELK, CloudWatch) to securely store logs and make them immutable. Set up real-time monitoring and alerts for suspicious activity – for example, large exports of records, off-hours access, or multiple failed logins. Automated alerts help catch breaches early. Remember, regulators explicitly look for whether you have logging and monitoring in place.
-
Conduct Risk Assessments & Penetration Testing. HIPAA mandates a thorough risk analysis of your ePHI environment. This means identifying vulnerabilities (unpatched servers, weak configs, third-party risks) and implementing mitigation. Treat risk assessment as an ongoing process: review it whenever you add features or services. Additionally, engage third-party security experts to perform penetration tests on your app, APIs, and infrastructure. While not explicitly required by HIPAA today, pen testing is industry best practice – catching flaws before attackers do. Many compliance audits expect evidence of regular testing. After tests, address findings promptly. As one guide warns, OCR “hates more than a HIPAA violation a HIPAA violation you didn’t even know happened” – strong reason to include proactive security testing in your development plan.
-
Sign Business Associate Agreements (BAAs). Before you go live, ensure BAAs are in place with any vendor touching PHI: cloud providers, third-party APIs, analytics firms, even email/text services if PHI passes through them. This legal contract makes the vendor a Business Associate and binds them to HIPAA standards. Maintain a register of all BAAs and review them regularly. If you integrate a new API or library that handles health data, check if HIPAA-protected, and if so, get a BAA or swap it out. This step is often overlooked by startups, but it’s foundational: an unsecured third party is a compliance gap. Without BAAs, both you and the vendor could face fines if PHI is mishandled.
Must-Have Features of a HIPAA-Compliant App
Building compliance isn’t just about infrastructure – your app itself should include features that protect PHI and meet regulatory requirements. Key features include:
-
Automatic Logoff / Session Timeout. The app should automatically log users out after a short period of inactivity (e.g. 5-15 minutes). This prevents unauthorized access if a device is left unattended.
-
Remote Wipe Capability. If the app runs on mobile devices, integrate Mobile Device Management (MDM) support so that lost or stolen devices can be wiped remotely. This ensures that even if a device is compromised, stored PHI is deleted.
-
Secure Backups. Have a robust backup system (the “3-2-1 rule”: 3 copies of data, 2 different media, 1 offsite) and ensure backups are encrypted. Regularly test your restore process. This protects availability of PHI and complies with contingency planning.
-
Consent Management. Include screens and audit trails for patient consent. For any sensitive operations (sharing data, telehealth sessions), record that the patient agreed. The Privacy Rule requires you to track authorizations for non-routine disclosures. Providing an easy way to view, sign, and revoke consents helps meet this requirement.
-
Audit Trails. Build in comprehensive audit logging that records every access or change to PHI within the app. This might include listing the user name, action taken, and timestamp. According to HIPAA’s Security Rule, audit controls are required to record and examine system activity involving PHI. Expose these logs to admins or compliance officers (in a readable format) so audits and investigations are feasible.
-
Data Retention Controls. Implement configurable retention periods. HIPAA requires keeping records (including logs) for at least six years, but you should also purge or archive data beyond retention limits to minimize risk. For example, auto-delete or anonymize old patient data that’s no longer needed for treatment.
-
Interoperability & Standards. While not strictly a HIPAA rule, using health data standards ensures secure integration. Support secure APIs and standards like HL7/FHIR for exchanging medical records. For example, use OAuth2 for authorizing API calls and follow FHIR security best practices. This makes it easier to work with EHR systems and ensures you’re using well-vetted protocols. Ensure any API you expose has rate limits and input validation to prevent data leaks.
By embedding these security and compliance features into your app’s design, you not only meet legal requirements but also demonstrate to users and regulators that you’ve built trust into the product from day one.
Also Read - How Much Does It Cost to Develop an App in 2026?
Tech Stack for HIPAA-Compliant App Development

Choosing the right technologies can simplify compliance:
-
Frontend: Many healthcare apps use cross-platform frameworks like React Native for faster development on both iOS and Android. Native options (Swift for iOS, Kotlin/Java for Android) offer full control and often better performance. Whatever you choose, use secure coding practices: avoid storing PHI on the device unless encrypted by the OS (Keychain/Keystore), disable screenshotting in sensitive views, and test for mobile-specific issues (push notifications shouldn’t reveal PHI on lock screens, etc.). For iOS and Android apps, our iOS and Android app development teams typically lock down these defaults by design.
-
Backend: A modern stack like Node.js or Python (Django/Flask) often powers healthcare apps. These platforms have mature libraries for encryption, authentication, and logging. Use frameworks’ security features (e.g. OWASP recommendations, CSRF protection) and keep dependencies up to date. For database, select a HIPAA-eligible option (e.g. encrypted PostgreSQL, MySQL, or DynamoDB on a compliant cloud).
-
Cloud & Security: As noted, use HIPAA-eligible cloud services only. AWS, Azure, and Google Cloud all offer managed databases, storage buckets, and messaging queues with encryption options. Leverage their security services: e.g. AWS KMS for keys, Security Groups/NACLs for network isolation, and CloudTrail/CloudWatch for logs. Use monitoring tools (Datadog, Splunk, etc.) that are approved under your BAA. In short, pick services explicitly tagged as compliant and ensure you configure them securely.
(Our software development solutions teams can advise on specific stacks and services. For example, AWS offers a “HIPAA Eligible” Services list and Azure has Healthcare Cloud for HIPAA offerings. Choose from these or similar lists to speed compliance.)
HIPAA Compliance Cost in 2026
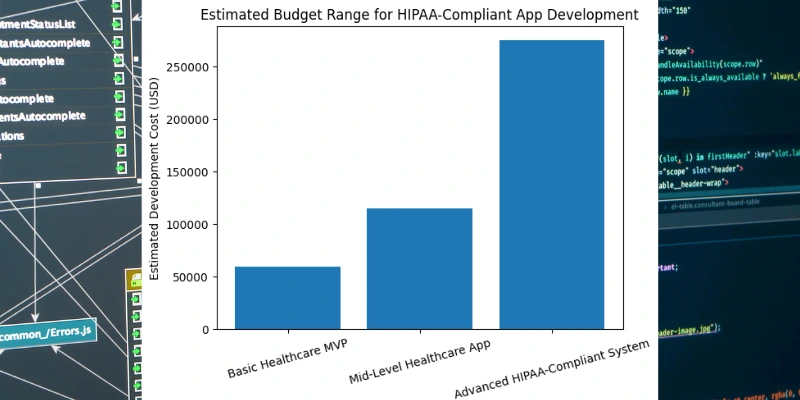
Budgeting for compliance is crucial. Developing a HIPAA-compliant app is significantly more expensive than a consumer app, due to added complexity and security requirements. According to industry estimates, basic healthcare MVP apps cost around $40,000–$80,000. A mid-level product (patient portals, simple telehealth) might run $80,000–$150,000. Advanced systems (EHRs, telemedicine with video/AI) can exceed $250,000–$300,000. These figures include design, development, and initial compliance work (encryption, architecture, risk analysis).
Key cost drivers include: complex security requirements, audit logging infrastructure, and professional services (legal review, compliance consultation). MVPs tend to cut features to limit scope, so an MVP-first approach saves money up front. Enterprise or fully-featured versions with full compliance stacks can easily reach the top end of the range.
Compliance tools & audits: In addition to development, plan for ongoing costs. Annual or quarterly security audits and penetration tests may add tens of thousands per year. Compliance management software (for risk tracking, policy management) and possibly hiring a HIPAA officer are other expenses.
Optimizing costs: To balance risk and budget, start with an MVP to test assumptions. Partner with an experienced healthcare development team – they’ll know how to integrate HIPAA controls efficiently. Avoid costly rework later by getting compliance right from the start. Also, use managed services (within BAA scopes) to offload heavy lifting; for example, AWS Lambda and managed databases can be more cost-effective than maintaining on-prem servers.
Common HIPAA Compliance Mistakes Startups Make
Even with the best intentions, many startups stumble on HIPAA pitfalls. Beware of these common errors:
-
“Cloud = Compliant” Fallacy: Simply hosting on a so-called “HIPAA-compliant” cloud doesn’t automatically make your app compliant. Founders often assume that because AWS or Azure will sign a BAA, their data is safe. In reality, the provider just enables compliance. You must configure encryption, access controls, and segmentation correctly. For example, leaving an S3 bucket public or failing to turn on encryption at rest (both common oversights) breaks HIPAA despite the BAA.
-
Using Non-HIPAA Tools: Integrating analytics or push services without checking compliance can leak PHI. For instance, adding a generic analytics SDK might send screen data or identifiers to a third party. As one guide warns, “mobile is where HIPAA compliance quietly dies” – caching PHI on the device or pushing medical info to unsecured channels are all major mistakes. Always vet third-party libraries: if they handle PHI, ensure a BAA or skip them.
-
Ignoring Logs & Backups: Some teams think logs and backups are low priority. In fact, OCR expects robust logging (tied to user IDs) and retention. Failing to log accesses (only logging logins, not actions) or keeping incomplete records can doom an audit. Likewise, skipping encrypted backups is dangerous; a ransomware attack could render unsaved data unrecoverable.
-
No Breach Response Plan: Too often, teams lack a clear incident response. Remember, HIPAA demands patient notifications within 60 days of discovery. Having no plan or legal templates means scrambling when every second counts. Develop and test your breach response procedure in advance – your compliance may depend on it.
By avoiding these pitfalls and embedding security into your development lifecycle, you greatly increase your chances of compliance and reduce the risk of costly errors.
HIPAA Compliance + AI, Telehealth & APIs (2026 Focus)
The rise of AI, telehealth, and interconnected devices adds new wrinkles to HIPAA compliance:
-
AI Model Risks: If your app uses AI (e.g. predictive diagnosis or chatbots), be careful with training data. Never feed PHI into a third-party AI service without safeguards – it could violate consent or cause inadvertent disclosure. For example, blocking PHI from being sent to public LLMs must be policy. Implement strict controls and logging when AI processes patient data, and validate outputs carefully for accuracy and privacy.
-
Telehealth & IoMT: Remote monitoring devices (wearables, home sensors) generate health data. Ensure any mobile/IoT data collection is encrypted end-to-end. Also, clarify data ownership and consent: patients must agree to telehealth data collection. For telehealth video/audio, use HIPAA-compliant conferencing (with proper encryption) and ensure recording (if any) is stored securely.
-
API Exposure Threats: Healthcare apps often expose APIs for integrations (e.g. scheduling, messaging). These are prime targets if misconfigured. Use secure authentication (OAuth2, short-lived tokens), validate all inputs, and rate-limit requests. Expose the minimum data via each API. In 2026, APIs for interoperability (FHIR, HL7) are common; make sure your FHIR endpoints enforce scope and consent, so a malicious app can’t harvest data.
Looking forward, future-proofing means building flexibility: design your system so you can quickly update encryption or access policies as standards evolve, and keep abreast of any new HIPAA guidance on AI or remote health tools.
Should You Build In-House or Hire Experts?
Deciding who builds your app is critical.
-
In-House Team: Building internally gives full control and may seem cheaper. However, HIPAA expertise is specialized. You’ll need developers, a security officer, and legal guidance. The risk: missing a detail because your team’s focus is on features, not compliance. Without prior experience, even small oversights (like misconfiguring a cloud database) can be costly.
-
Freelancers: Avoid relying solely on freelancers for a HIPAA app. They may lack accountability and HIPAA know-how, and managing BAA and compliance processes across ad-hoc contractors is difficult.
-
Dedicated App Development Company: A reputable healthcare app developer or IT vendor brings relevant experience. They typically know the regulatory checklist, security best practices, and have vetted processes. For example, a mobile app development company with healthcare expertise can handle the end-to-end project: design, coding, security audit, documentation. They also often offer consulting services. In places like the UAE, specialized firms (e.g. those offering HIPAA consulting in UAE) can help navigate international deployment.
Ultimately, partnering with experts can accelerate development and reduce risk. They’ll help ensure your app is “audit-ready” from launch – a worthwhile tradeoff for many startups seeking to avoid expensive missteps.
Final Checklist – Is Your App HIPAA Compliant?
Before launch, quickly verify these essentials:
-
✔ Encryption Everywhere: Data encrypted in transit (TLS) and at rest (disk/db encryption).
-
✔ Access Controls: Unique logins, MFA enabled, least-privilege roles.
-
✔ Audit Logs: Detailed, tamper-proof logs stored for 6+ years.
-
✔ Business Associate Agreements (BAAs): Signed with all PHI-handling vendors.
-
✔ Incident Response Plan: Documented breach plan, with notification workflow.
-
✔ Secure Backups: Regularly tested, encrypted backups of PHI.
-
✔ Risk Assessment: Completed HIPAA Security Rule risk analysis and mitigation plan.
If you can check off every item above, your app is on strong footing. If gaps remain, address them before going live – HIPAA enforcement won’t wait.
Conclusion: Build Trust, Not Just an App
In 2026, HIPAA compliance isn’t just a legal checkbox – it’s a foundation of trust and growth for any healthcare venture. By rigorously protecting patient data, you not only avoid fines and breaches but also signal credibility to users and partners. In fact, strong privacy and security are competitive advantages: a demonstrably secure, compliant app will attract more patients and contracts than one with uncertain safeguards. Think of HIPAA not just as regulation, but as a pledge to users that their health data is safe. Compliance done well can fuel growth, partnerships, and brand reputation.
Ready to build a secure, compliant healthcare app? With the right approach – from healthcare software services to a dedicated compliance plan – you can turn HIPAA obligations into a shield that protects your users and your business.